Since OSFI’s new B-10 Guideline took effect May 1, 2024, Canadian federally regulated financial institutions (FRFIs) have invested an average of $2.3 million implementing comprehensive third-party risk management frameworks. Yet according to OSFI’s own guidance, 68% of institutions still struggle with the fundamental shift from materiality-based to risk-and-criticality assessments.
The new OSFI B-10 Third Party Risk Management Guideline represents the most significant change to Canadian financial institution oversight in over a decade. Unlike the previous outsourcing-focused approach, this framework requires FRFIs to manage risks across all third-party arrangements—from critical cloud services to utility providers. For institutions navigating Canada’s complex regulatory landscape, understanding these requirements is essential for maintaining operational resilience and regulatory compliance. This comprehensive framework directly supports broader GRC compliance strategies for Canadian financial institutions.
This guide examines the six expected outcomes, eleven principles, and practical requirements that define OSFI’s new approach to third-party risk management. You’ll understand how to assess risk and criticality, build governance frameworks, and meet technology-specific requirements that protect your institution’s operational and financial resilience.
What is OSFI B-10 Third Party Risk Management? (New vs. Old Requirements)
OSFI B-10 Third Party Risk Management is a comprehensive regulatory framework requiring Canadian FRFIs to identify, assess, and manage risks arising from all third-party arrangements through enterprise-wide governance and risk-based controls proportionate to each arrangement’s risk and criticality.
The transformation from the old to new B-10 represents a fundamental shift in regulatory thinking. The previous guideline, last updated in 2009, focused narrowly on “material outsourcing arrangements.” Today’s framework encompasses every third-party relationship that could impact institutional resilience.
Key Changes at a Glance
| Old B-10 (2009) | New B-10 (2024) |
| Material outsourcing only | All third-party arrangements |
| Binary materiality threshold | Risk and criticality assessment |
| Limited governance requirements | Enterprise-wide TPRMF mandate |
| Basic contractual provisions | Comprehensive risk management |
| Technology risks addressed minimally | Dedicated technology section |
Scope Expansion: The new guideline covers independent professionals, brokers, utilities, financial market infrastructures, cloud providers, and even affiliate relationships. This expansion means FRFIs must now evaluate hundreds or thousands of relationships previously outside regulatory scope.
Assessment Methodology: Rather than asking “Is this material?” institutions now assess “What is the risk and criticality?” This nuanced approach allows proportionate risk management while ensuring comprehensive coverage.
Governance Requirements: The new framework mandates a Third Party Risk Management Framework (TPRMF) spanning the entire relationship lifecycle from sourcing through exit planning.
The regulatory intent is clear: as FRFIs increasingly rely on complex third-party ecosystems, risk management must evolve to match operational reality.
The 6 Expected Outcomes and 11 Principles Framework Explained
OSFI’s outcomes-based approach establishes clear expectations while allowing implementation flexibility. The six expected outcomes represent the regulatory destination, while eleven supporting principles provide the roadmap for achieving compliance.
The Six Expected Outcomes
Outcome 1: Governance and accountability structures are clear with comprehensive risk management strategies and frameworks in place.
This outcome demands enterprise-wide visibility into third-party risks. FRFIs must establish clear roles, responsibilities, and decision-making authority. Senior management remains accountable for all outsourced activities, requiring robust oversight mechanisms and regular reporting.
Outcome 2: Risks posed by third parties are identified and assessed.
Comprehensive risk identification goes beyond traditional operational risks. FRFIs must evaluate financial, reputational, strategic, concentration, and emerging risks. Assessment methodologies must be documented, consistent, and regularly updated to reflect changing risk landscapes.
Outcome 3: Risks posed by third parties are managed and mitigated within the FRFI’s Risk Appetite Framework.
Risk mitigation must align with institutional risk appetite. This requires documented risk acceptance decisions, mitigation strategies, and escalation procedures. Controls must be proportionate to risk levels while ensuring adequate protection.
Outcome 4: Third party performance is monitored and assessed, and risks and incidents are proactively addressed.
Ongoing monitoring replaces point-in-time assessments. FRFIs need real-time visibility into third-party performance, financial health, and risk indicators. Incident management processes must enable rapid response and remediation.
Outcome 5: The FRFI’s third-party risk management program allows the FRFI to identify and manage a range of third-party relationships on an ongoing basis.
This outcome emphasizes program scalability and sustainability. Risk management processes must handle diverse relationship types while maintaining consistent standards. Regular program reviews ensure continuous improvement.
Outcome 6: Technology and cyber operations carried out by third parties are transparent, reliable and secure.
Technology risks receive dedicated attention reflecting their critical importance. FRFIs must ensure third-party technology operations meet institutional standards for security, reliability, and transparency. This includes cloud-specific requirements and portability considerations.
Supporting Principles Framework
The eleven principles translate outcomes into actionable guidance:
- Principles 1-2: Establish accountability and framework requirements
- Principles 3-5: Address risk identification, due diligence, and subcontractor management
- Principles 6-9: Cover contractual requirements, data security, audit rights, and business continuity
- Principles 10-11: Focus on monitoring and incident management
This structure ensures comprehensive risk management while maintaining operational flexibility.
Understanding Risk and Criticality Assessment (The Core Change)
The shift from materiality to risk-and-criticality assessment represents B-10’s most significant conceptual change. This new methodology enables proportionate risk management while ensuring comprehensive coverage.
Defining Criticality
Criticality denotes importance to the FRFI’s operations, strategy, financial condition, or reputation. It emphasizes impact regardless of likelihood. Critical arrangements provide goods or services that, if disrupted, could threaten continued operation, safety and soundness, or financial system role.
When determining criticality, FRFIs should consider:
- Severity of loss if the third party fails to meet expectations
- Substitutability including portability and transfer timelines
- Degree of support for critical FRFI operations
- Business impact if exit and transition become necessary
Risk Assessment Criteria
Risk assessment evaluates the probability of negative outcomes. Key factors include:
- Financial health of the third party and potential step-in risks
- Operational resilience including business continuity capabilities
- Regulatory compliance ability and track record
- Information security practices and cyber risk management
- Subcontractor dependencies and supply chain complexity
- Geographic concentration and geopolitical risks
Practical Scoring Framework
Many FRFIs adopt matrix-based approaches combining criticality and risk scores:
High Criticality + High Risk: Maximum oversight including board reporting, detailed contracts, regular audits, and comprehensive monitoring.
High Criticality + Low Risk: Moderate oversight with emphasis on monitoring and contingency planning.
Low Criticality + High Risk: Risk-focused management with mitigation strategies and performance monitoring.
Low Criticality + Low Risk: Basic oversight with periodic reviews and standard contractual protections.
Common Assessment Mistakes
Mistake 1: Confusing materiality with criticality. Materiality focuses on financial significance; criticality emphasizes operational impact.
Mistake 2: Static assessments. Risk and criticality change over time requiring regular reassessment.
Mistake 3: Inconsistent methodology. Different business units using different criteria creates compliance gaps.
Mistake 4: Inadequate documentation. Assessment rationale must be documented for regulatory review.
The risk-and-criticality framework enables nuanced risk management while ensuring no arrangement escapes appropriate oversight.
Third Party Risk Management Framework (TPRMF) Implementation
The TPRMF serves as the architectural foundation for enterprise-wide third-party risk management. This framework must span the complete relationship lifecycle while providing consistent governance across all business units.
Enterprise-Wide Framework Requirements
Governance Structure: The TPRMF requires clear accountability starting with board oversight and cascading through senior management to operational teams. Risk committees must receive regular reporting on third-party risk exposures and emerging trends.
Policy Integration: Third-party risk policies must align with enterprise risk management frameworks and risk appetite statements. Policies should address risk identification, assessment, mitigation, monitoring, and reporting requirements.
Lifecycle Management: The framework must address six key lifecycle stages:
- Sourcing and Selection: Risk-informed vendor selection with appropriate due diligence
- Contracting: Risk-appropriate contractual protections and service levels
- Onboarding: Validation of controls and integration planning
- Monitoring: Ongoing performance and risk surveillance
- Management: Incident response and relationship optimization
- Exit Planning: Transition strategies and business continuity
Roles and Responsibilities Framework
Board of Directors: Provides oversight of third-party risk strategy and appetite. Reviews significant risk exposures and incidents.
Senior Management: Ensures effective TPRMF implementation and operation. Approves material third-party arrangements and risk acceptance decisions.
Risk Management: Develops risk assessment methodologies and monitors aggregate exposures. Provides independent challenge and reporting.
Business Units: Manages day-to-day third-party relationships within established risk parameters. Conducts ongoing monitoring and performance management.
Legal and Compliance: Ensures contractual adequacy and regulatory compliance. Reviews arrangements for legal and regulatory risks.
Information Technology: Manages technology risks and security requirements. Oversees cloud arrangements and cyber risk controls.
Technology Integration Considerations
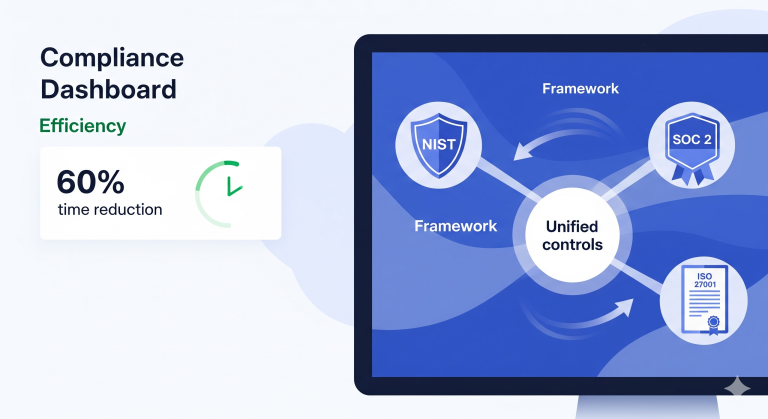
Modern TPRMFs require technology platforms supporting:
- Centralized Inventory: Single source of truth for all third-party relationships
- Risk Assessment Tools: Standardized methodologies and scoring models
- Workflow Management: Automated processes for approvals and reviews
- Monitoring Dashboards: Real-time visibility into performance and risks
- Reporting Capabilities: Regular and ad-hoc reporting for management and regulators
- Document Management: Centralized storage for contracts, assessments, and communications
Successful TPRMF implementation requires sustained executive commitment, adequate resources, and cultural change supporting enterprise-wide risk management.
Due Diligence and Contractual Requirements (Annex 1 & 2 Breakdown)
OSFI’s annexes provide detailed guidance on due diligence factors and contractual provisions. These requirements scale with risk and criticality levels, ensuring proportionate but comprehensive coverage.
Annex 1: Due Diligence Factors
For high-risk and critical arrangements, FRFIs must evaluate numerous factors:
Operational Capabilities: Experience, technical competence, and capacity for service delivery. This includes evaluating track records, certifications, and resource adequacy.
Financial Strength: Financial stability and ability to deliver contracted services. Analysis should include financial statements, credit ratings, and business sustainability.
Risk Management: Strength of third-party risk management programs and alignment with FRFI requirements. Evaluation includes policies, procedures, and control effectiveness.
Regulatory Compliance: Adherence to applicable laws and regulations in relevant jurisdictions. This includes compliance history and regulatory standing.
Information Security: Cybersecurity programs and practices including incident response capabilities. Assessment should cover security frameworks and testing results.
Business Continuity: Disaster recovery and business continuity capabilities including testing frequency and results. Plans should address severe but plausible scenarios.
Subcontractor Management: Third-party’s ability to manage its own third-party relationships and associated risks.
Geographic Considerations: Political, legal, and operational risks associated with service locations and subcontractor jurisdictions.
Annex 2: Contractual Provisions
High-risk and critical arrangements require comprehensive contractual protections:
Service Definition: Clear scope, performance measures, and service level agreements. Contracts should specify deliverables, timelines, and quality standards.
Roles and Responsibilities: Detailed allocation of responsibilities between parties including technology and cyber risk management.
Subcontractor Management: Notification requirements, approval rights, and due diligence capabilities for subcontractor arrangements.
Data Security: Comprehensive data protection requirements including confidentiality, integrity, and availability protections.
Audit Rights: FRFI and OSFI rights to conduct or commission audits of third-party operations and controls.
Incident Reporting: Timely notification requirements for incidents affecting service delivery or FRFI operations.
Business Continuity: Service continuation requirements during disruptions and testing obligations.
Termination and Exit: Clear termination triggers, notification periods, and data return requirements.
Managing Standardized Contracts
Many third parties offer standardized contracts with limited negotiation flexibility. OSFI recognizes these limitations while maintaining risk management expectations.
Risk Assessment: Evaluate inherent risks and available mitigating controls when standardization limits contractual protections.
Alternative Controls: Develop redundancies, workarounds, and monitoring mechanisms to address contractual limitations.
Formal Risk Acceptance: Document risk acceptance decisions for standardized contract limitations.
Enhanced Monitoring: Implement additional oversight when contractual protections are limited.
The key is ensuring adequate risk management even when traditional contractual risk transfer is unavailable.
Technology and Cyber Risk Management (Section 4 Deep Dive)
Technology and cyber risks receive dedicated attention in B-10 reflecting their critical importance to financial institution operations. These requirements complement OSFI’s B-13 Technology and Cyber Risk Management Guideline.
Technology Risk Framework
Clear Accountability: Roles and responsibilities for technology controls must be explicitly defined between FRFIs and third parties. This includes configuration management, access controls, and security monitoring.
Standards Compliance: Third parties must comply with FRFI technology standards or recognized industry frameworks. This ensures consistent security baselines across all technology relationships.
Control Validation: FRFIs must verify third-party technology controls through audits, certifications, or continuous monitoring.
Cloud-Specific Requirements
Cloud arrangements require additional considerations:
Strategic Approach: Cloud adoption must align with institutional strategy and risk appetite. Ad-hoc cloud usage creates ungoverned risks.
Portability Assessment: FRFIs must evaluate data and application portability between cloud providers. This assessment should consider technical feasibility, costs, and timeframes.
Multi-Cloud Strategies: Consider diversification strategies to reduce concentration risk while balancing operational complexity.
Data Protection: Enhanced data security requirements reflecting cloud-specific risks including data residency and access controls.
Integration with OSFI B-13
B-10 technology requirements complement B-13 expectations:
Incident Reporting: Third-party incidents must be reported according to OSFI’s Technology and Cyber Security Incident Reporting Advisory.
Risk Management: Technology risk management must align with B-13 governance and control requirements.
Resilience Planning: Business continuity planning must address technology dependencies and recovery capabilities.
Canadian Data Considerations
Data Residency: Canadian data residency requirements may apply depending on data types and regulatory obligations.
Cross-Border Access: Arrangements involving data storage or processing outside Canada require careful legal and risk analysis.
Regulatory Access: OSFI must maintain unimpeded access to FRFI data regardless of hosting location.
Technology risk management requires specialized expertise and ongoing attention as threats and technologies evolve rapidly.
Implementation Timeline and Transition Planning (Practical Roadmap)
Successful B-10 implementation requires structured project management addressing organizational, process, and technology changes. Most FRFIs need 12-18 months for comprehensive implementation.
Phase 1: Assessment and Planning (Months 1-3)
Gap Analysis: Compare current capabilities against B-10 requirements. Identify specific gaps in governance, processes, technology, and resources.
Stakeholder Engagement: Establish project governance including executive sponsorship, steering committee, and working groups.
Resource Planning: Determine internal resources and external support requirements including technology investments and consulting needs.
Project Roadmap: Develop detailed implementation plan with milestones, dependencies, and success criteria.
Phase 2: Framework Development (Months 4-8)
Policy Development: Create or update third-party risk management policies aligned with B-10 requirements and institutional risk appetite.
Process Design: Develop standardized processes for risk assessment, due diligence, contracting, monitoring, and incident management.
Technology Selection: Evaluate and implement technology platforms supporting TPRMF requirements.
Training Programs: Develop training materials and conduct initial staff training on new requirements and processes.
Phase 3: Pilot Implementation (Months 9-12)
Pilot Arrangements: Test new processes with selected third-party arrangements across different risk levels and business units.
Process Refinement: Adjust processes based on pilot experience and lessons learned.
Change Management: Address organizational resistance and cultural barriers to new risk management approaches.
Documentation: Complete policy documentation, procedure manuals, and training materials.
Phase 4: Full Rollout (Months 13-18)
Enterprise Deployment: Roll out new processes across all business units and third-party arrangements.
Legacy Arrangement Review: Systematically review and update existing arrangements to meet B-10 standards.
Monitoring and Reporting: Implement ongoing monitoring and reporting capabilities.
Continuous Improvement: Establish feedback mechanisms and regular program reviews.
Common Implementation Challenges
Resource Constraints: B-10 implementation requires significant resources often competing with other priorities.
Cultural Resistance: Traditional procurement and vendor management cultures may resist comprehensive risk management approaches.
Technology Integration: Existing technology systems may not support comprehensive third-party risk management requirements.
Legacy Contracts: Existing contracts may lack required provisions and may not be amendable until renewal.
Coordination Complexity: Enterprise-wide implementation requires coordination across multiple business units and functions.
Success requires sustained executive commitment, adequate resources, and structured change management.
OSFI B-10 Compliance Costs and ROI (2025 Budget Planning)
Understanding implementation and ongoing costs helps FRFIs plan budgets and demonstrate compliance value. Costs vary significantly based on institutional size, complexity, and current capabilities.
Implementation Cost Categories
Technology Investments: Third-party risk management platforms typically cost $200,000-$2,000,000 depending on institutional size and feature requirements. Additional integration costs may apply.
Consulting Services: External support for gap analysis, framework development, and implementation typically ranges from $500,000-$3,000,000 based on scope and timeline.
Internal Resources: Dedicated project teams typically include 5-15 full-time equivalent staff for 12-18 months representing $750,000-$2,250,000 in internal costs.
Training and Change Management: Comprehensive training programs typically cost $100,000-$500,000 including materials development and delivery.
Process Documentation: Policy development, procedure creation, and documentation typically requires $150,000-$400,000 in internal and external resources.
Ongoing Operational Costs
Technology Maintenance: Annual platform maintenance and licensing typically costs 15-20% of initial technology investment.
Additional Staffing: Most FRFIs add 3-8 dedicated third-party risk management staff representing $300,000-$800,000 annually.
External Audits: Enhanced third-party auditing typically costs $200,000-$600,000 annually depending on third-party portfolio size.
Ongoing Training: Annual training and certification programs typically cost $50,000-$150,000.
Cost by Institution Size
Large FRFIs (>$100B assets): Total implementation costs typically range from $5-$15 million with ongoing costs of $2-$5 million annually.
Mid-Size FRFIs ($10-$100B assets): Implementation costs typically range from $2-$8 million with ongoing costs of $800,000-$2.5 million annually.
Smaller FRFIs (<$10B assets): Implementation costs typically range from $500,000-$3 million with ongoing costs of $200,000-$1 million annually.
Return on Investment
Regulatory Compliance: Avoiding regulatory sanctions and reputational damage provides substantial but difficult-to-quantify returns.
Operational Resilience: Enhanced third-party oversight reduces operational disruptions and associated costs.
Vendor Performance: Improved vendor management often yields cost savings and service improvements.
Risk Reduction: Better risk management reduces potential losses from third-party failures.
Strategic Value: Enhanced third-party governance supports strategic initiatives and digital transformation.
Most FRFIs achieve positive ROI within 3-5 years through combination of risk reduction and operational improvements.
Conclusion
OSFI’s B-10 Third Party Risk Management Guideline fundamentally transforms how Canadian FRFIs approach third-party relationships. The shift from material outsourcing to comprehensive risk management reflects the modern reality of complex third-party ecosystems supporting critical financial services.
The framework’s six outcomes and eleven principles provide clear direction while allowing implementation flexibility. Success requires enterprise-wide commitment to risk-based thinking, proportionate controls, and continuous improvement. FRFIs must invest in governance structures, risk assessment capabilities, and monitoring systems proportionate to their third-party dependencies.
Technology risks receive particular attention reflecting their critical importance and elevated threat landscape. Cloud arrangements, cyber security, and incident reporting requirements demand specialized attention and expertise.
Implementation represents a significant undertaking requiring 12-18 months and substantial investment. However, institutions benefit from enhanced operational resilience, improved vendor performance, and stronger regulatory compliance supporting long-term success in Canada’s evolving financial services landscape.
For comprehensive guidance on building enterprise-wide compliance programs encompassing B-10 requirements and other Canadian regulatory obligations, explore our complete GRC compliance framework for Canadian financial institutions.