According to IBM’s 2024 Cost of a Data Breach Report, organizations without regular IT audits experience security incidents costing an average of $4.45 million—significantly higher than companies with established audit processes. This alarming statistic highlights why understanding the IT audit process has become critical for modern businesses navigating increasingly complex technological environments.
The IT audit process is a systematic examination of an organization’s information technology infrastructure, controls, and procedures designed to assess security, compliance, and operational effectiveness. Unlike one-time assessments, this process provides ongoing evaluation of IT systems to identify vulnerabilities before they become costly problems. When conducted by qualified IT auditors, this methodology helps organizations maintain regulatory compliance, strengthen cybersecurity posture, and optimize technology investments.
This guide outlines the proven step-by-step methodology that professional auditors use to evaluate IT environments systematically. You’ll discover the essential frameworks, actionable checklists, and implementation strategies that ensure comprehensive audit coverage while delivering measurable business value.
Understanding the IT Audit Process Foundation
The IT audit process is a structured methodology that evaluates an organization’s information technology systems, controls, and governance to ensure they effectively support business objectives while managing risks appropriately. This systematic approach examines everything from network security and data protection to compliance adherence and operational efficiency.
At its core, the IT audit process follows a six-phase framework that builds upon established industry standards like COBIT and NIST guidelines. These phases include planning and scoping, risk assessment, controls evaluation, compliance review, technical testing, and reporting with remediation planning. Each phase serves a specific purpose while contributing to the overall audit objective of providing assurance about IT effectiveness.
The process differs significantly from project-based assessments because it establishes ongoing evaluation cycles rather than one-time examinations. This continuous approach allows organizations to adapt to evolving threats, changing regulations, and emerging technologies. Regular IT audit processes help businesses maintain security posture, demonstrate compliance to stakeholders, and identify optimization opportunities.
Modern IT audit processes integrate risk-based approaches that prioritize high-impact areas over comprehensive system reviews. This methodology ensures audit resources focus on the most critical vulnerabilities and business risks. The framework also emphasizes evidence-based findings, requiring auditors to document observations with supporting materials that can withstand regulatory scrutiny.
Successful IT audit processes align closely with organizational objectives and regulatory requirements. They consider industry-specific compliance needs, business continuity requirements, and strategic technology initiatives. This alignment ensures audit findings provide actionable insights that drive meaningful improvements rather than academic observations.
Phase 1 – Planning and Scoping Your IT Audit
Effective IT audit planning establishes the foundation for successful engagements by defining clear objectives, boundaries, and resource requirements. The planning phase typically consumes 15-20% of total audit time but significantly impacts overall audit quality and efficiency.
The first step involves defining audit objectives based on business risks, regulatory requirements, and stakeholder expectations. These objectives should specify what the audit aims to accomplish, such as evaluating SOC 2 compliance, assessing cybersecurity controls, or reviewing cloud migration security. Clear objectives help auditors focus their efforts and communicate expectations to audit clients.
Scope definition determines which systems, processes, and locations the audit will examine. Effective scoping considers system criticality, risk exposure, and available resources. For example, a financial services audit might prioritize payment processing systems and customer data repositories while deferring lower-risk administrative systems. Proper scoping prevents scope creep while ensuring adequate coverage of high-risk areas.
Resource planning addresses team composition, timeline development, and budget allocation. Audit teams typically require diverse skills including technical expertise, regulatory knowledge, and industry experience. Timeline planning should account for system availability, business cycles, and reporting deadlines. Many organizations schedule audits during low-activity periods to minimize business disruption.
Stakeholder engagement during planning ensures audit objectives align with management expectations and regulatory requirements. This involves meeting with IT leadership, compliance teams, and business stakeholders to understand current challenges and priorities. Early engagement also helps identify potential obstacles and establishes communication protocols for the audit process.
The planning phase concludes with documented audit programs that specify testing procedures, evidence requirements, and evaluation criteria. These programs serve as roadmaps for fieldwork while ensuring consistent application of audit standards. Well-developed audit programs also facilitate quality reviews and knowledge transfer between team members.
Phase 2 – Risk Assessment and Prioritization Framework
Risk assessment forms the strategic foundation of effective IT audit processes by identifying and prioritizing the most significant threats to organizational objectives. This phase transforms broad audit scope into focused testing areas based on potential impact and likelihood of occurrence.
The risk assessment process begins with threat identification across multiple categories including cybersecurity risks, compliance violations, operational disruptions, and technology obsolescence. Auditors examine internal and external threat sources such as malicious attacks, human error, system failures, and regulatory changes. This comprehensive view ensures no significant risk categories are overlooked during planning.
Risk evaluation involves assessing both the probability and potential impact of identified threats. High-probability, high-impact risks receive priority attention during subsequent audit phases. For example, outdated security patches on internet-facing systems typically warrant immediate examination, while minor configuration issues on internal systems might receive lower priority. This prioritization ensures audit resources focus on areas with greatest business impact.
Industry-specific risk considerations significantly influence assessment outcomes. Healthcare organizations must prioritize HIPAA compliance and patient data protection, while financial services firms focus on SOX controls and payment card security. Manufacturing companies emphasize operational technology security and supply chain risks. Understanding these industry nuances helps auditors identify relevant risk factors that generic assessments might miss.
Technology architecture analysis examines how system design and integration create risk exposure. Cloud environments introduce shared responsibility considerations, legacy systems present security and maintenance challenges, and third-party integrations create vendor management risks. Modern IT environments often combine multiple architectural approaches, requiring auditors to understand complex interdependencies and potential failure points.
The risk assessment culminates in a prioritized testing plan that allocates audit effort based on risk exposure rather than system inventory. This approach ensures high-risk areas receive thorough examination while lower-risk systems undergo more limited testing. Risk-based planning also helps auditors explain testing decisions to management and regulatory bodies when questions arise about audit scope.
Phase 3 – Controls Evaluation and Testing
Controls evaluation examines the design and operating effectiveness of IT controls that protect organizational assets and support business processes. This phase determines whether implemented controls adequately address identified risks and operate consistently over time.
IT controls fall into three primary categories: preventive controls that stop problems before they occur, detective controls that identify issues after they happen, and corrective controls that fix problems once detected. Preventive controls include access restrictions, system configurations, and approval workflows. Detective controls encompass monitoring systems, log reviews, and exception reports. Corrective controls involve incident response procedures, backup recovery processes, and system patching protocols.
Testing methodologies vary based on control types and audit objectives. Inquiry involves interviewing control owners to understand procedures and responsibilities. Observation means watching control execution during normal operations. Inspection examines control documentation, system configurations, and evidence of control operation. Re-performance involves auditors independently executing control procedures to verify effectiveness.
Evidence collection requirements support audit conclusions with documented proof of control operation or failure. Strong evidence includes system-generated logs, approved documents, and independent confirmations. Weak evidence relies on management representations or incomplete documentation. Professional auditing standards require sufficient, appropriate evidence to support all audit findings and conclusions.
Common control failures include inadequate access restrictions, missing approvals, incomplete monitoring, and delayed responses to identified issues. These failures often result from poor control design, insufficient training, or inadequate monitoring. Identifying failure patterns helps organizations address root causes rather than individual symptoms.
Control testing results inform overall risk assessments and guide remediation priorities. Effective controls reduce residual risk levels, while control deficiencies increase risk exposure. This relationship between control effectiveness and risk helps auditors provide meaningful recommendations that address the most significant vulnerabilities first.
Phase 4 – Compliance Review and Regulatory Alignment
Compliance review verifies that organizational practices meet applicable legal, regulatory, and industry standard requirements. This phase requires detailed knowledge of relevant frameworks and their specific implementation requirements.
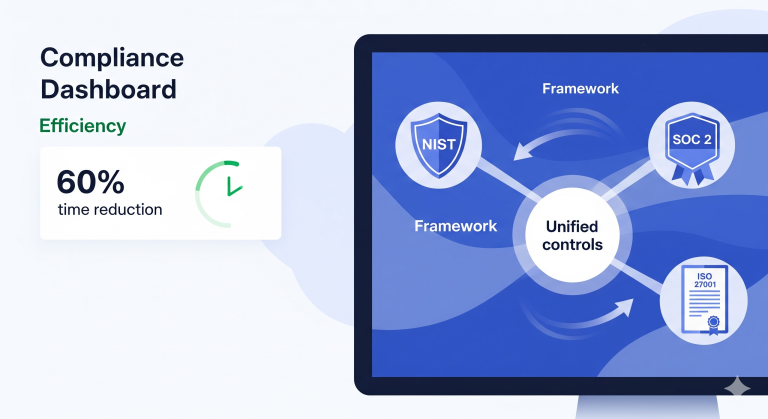
Major compliance frameworks each address different risk areas and stakeholder needs. SOC 2 examines service organization controls related to security, availability, processing integrity, confidentiality, and privacy. ISO 27001 provides comprehensive information security management requirements. NIST frameworks offer cybersecurity and risk management guidance. Industry-specific regulations like HIPAA, GDPR, and PCI DSS address sector-specific protection requirements.
Compliance testing procedures verify both policy existence and practical implementation. Policy reviews examine whether documented procedures address regulatory requirements comprehensively. Implementation testing determines whether employees actually follow established policies during daily operations. This dual approach identifies gaps between written policies and actual practices that could create compliance violations.
Documentation requirements vary significantly across regulatory frameworks but generally include policies, procedures, training records, incident logs, and regular assessment reports. Auditors must verify that documentation exists, remains current, and demonstrates ongoing compliance activities. Missing or outdated documentation often indicates compliance program weaknesses that require management attention.
Gap analysis methodology compares current practices against regulatory requirements to identify specific deficiencies. This systematic comparison helps organizations understand compliance status and prioritize improvement efforts. Gap analysis also supports compliance roadmap development by identifying specific actions needed to achieve full compliance.
Compliance review findings require careful documentation because they often influence regulatory reporting and legal liability. Auditors must clearly distinguish between actual violations and best practice recommendations. This distinction helps organizations allocate resources appropriately and communicate compliance status accurately to stakeholders and regulators.
Phase 5 – Technical Testing and Vulnerability Assessment
Technical testing evaluates the security and functionality of IT systems through hands-on examination of networks, applications, and infrastructure components. This phase often reveals vulnerabilities that policy reviews and interviews cannot detect.
Network security testing examines firewall configurations, intrusion detection systems, and access controls that protect organizational networks from unauthorized access. Testing includes reviewing firewall rules for appropriate restrictions, verifying that monitoring systems detect suspicious activity, and confirming that network segmentation limits potential attack spread. These technical tests often identify configuration errors that create security exposures.
Access control testing verifies that user permissions align with job responsibilities and organizational policies. This includes examining user account provisioning processes, reviewing privileged access controls, and testing account termination procedures. Technical testing might involve attempting unauthorized access to verify that controls prevent inappropriate system use.
Vulnerability scanning uses automated tools to identify known security weaknesses in systems and applications. These scans check for missing security patches, default configurations, and common vulnerabilities. However, scan results require expert interpretation because automated tools often generate false positives and may miss sophisticated attack vectors.
Penetration testing simulates real-world attacks to evaluate how effectively security controls prevent unauthorized access. Unlike vulnerability scanning, penetration testing involves active attempts to exploit identified weaknesses. This testing provides realistic assessment of security effectiveness but requires careful planning to avoid disrupting business operations.
Technical testing limitations include point-in-time snapshots that may not reflect ongoing security posture, potential business disruption from active testing, and skill requirements that exceed typical audit team capabilities. Organizations should understand these limitations when interpreting technical testing results and planning remediation activities.
The technical testing phase concludes with prioritized vulnerability lists that help organizations focus remediation efforts on the most critical exposures. This prioritization considers factors like vulnerability severity, system exposure, and potential business impact. Effective prioritization helps organizations achieve maximum security improvement with limited resources.
Phase 6 – Reporting and Remediation Planning
Audit reporting transforms technical findings into actionable business recommendations that drive organizational improvement. Effective reports communicate complex technical issues in language that management can understand and act upon.
Executive summaries provide high-level overviews of audit results for senior management and board members. These summaries should highlight the most significant findings, overall risk ratings, and critical action items. Executive summaries typically avoid technical details while emphasizing business impact and resource requirements for recommended improvements.
Finding classification helps organizations prioritize remediation efforts by categorizing issues based on severity and urgency. Critical findings require immediate attention because they create significant security or compliance risks. High-priority findings need prompt remediation but may allow brief delays for resource planning. Medium and low-priority findings can often be addressed during regular system maintenance cycles.
Remediation roadmaps provide structured approaches for addressing identified issues systematically. These roadmaps sequence remediation activities based on dependencies, resource requirements, and risk reduction potential. For example, implementing centralized access management might need to precede detailed user access reviews because centralization simplifies the review process.
Management responses document organizational commitments to address audit findings within specified timeframes. These responses should include specific actions, responsible parties, and target completion dates. Clear management responses facilitate follow-up activities and demonstrate organizational commitment to addressing identified issues.
Follow-up procedures ensure that planned remediation activities actually occur and effectively address identified issues. Many audit standards require formal follow-up processes that verify completion and effectiveness of management responses. This follow-up helps organizations realize the benefits of audit investments while demonstrating continuous improvement to stakeholders.
Audit reports often serve multiple audiences including management, regulators, and external stakeholders. Report format and content should consider these different audiences while maintaining technical accuracy and professional standards. Well-crafted reports enhance audit value by facilitating understanding and action across diverse stakeholder groups.
Advanced IT Audit Strategies and Emerging Trends
Modern IT audit approaches increasingly incorporate advanced technologies and methodologies that enhance audit effectiveness while reducing time and resource requirements. These emerging strategies help organizations adapt audit processes to rapidly evolving technology environments.
Continuous auditing models replace periodic assessments with ongoing monitoring that provides real-time visibility into control effectiveness and risk exposure. These models use automated data collection and analysis to identify issues as they occur rather than months later during scheduled audits. Continuous auditing particularly benefits organizations with dynamic IT environments where traditional periodic audits may miss rapidly changing risk conditions.
Automation and artificial intelligence are transforming traditional audit procedures by handling routine data collection and analysis tasks. Automated tools can examine user access patterns, analyze log files, and identify unusual system behaviors more efficiently than manual procedures. However, automation requires careful implementation to ensure that automated procedures adequately address audit objectives and regulatory requirements.
Cloud audit considerations address unique challenges created by shared infrastructure, distributed data storage, and complex vendor relationships. Cloud audits must evaluate shared responsibility models, vendor security controls, and data location requirements. Multi-cloud environments add additional complexity by requiring auditors to understand different vendor approaches and integration risks.
DevOps and agile development practices create new audit challenges by accelerating change cycles and blurring traditional control boundaries. Auditors must understand continuous integration pipelines, automated deployment processes, and dynamic infrastructure management. These environments require audit approaches that can evaluate controls embedded in development processes rather than separate operational procedures.
Future-proofing audit programs involves developing capabilities that can adapt to emerging technologies and evolving risk landscapes. This includes training audit staff on new technologies, establishing relationships with specialized service providers, and developing flexible audit methodologies that can accommodate new system types and business models.
Organizations implementing advanced audit strategies should maintain balance between innovation and proven practices. While new technologies offer significant benefits, they also introduce implementation risks that require careful management. Successful organizations typically pilot advanced approaches on limited scope before full implementation across their audit programs.
Conclusion
The IT audit process provides organizations with systematic methodology for evaluating technology risks, ensuring compliance, and optimizing system effectiveness. This six-phase framework—planning, risk assessment, controls evaluation, compliance review, technical testing, and reporting—creates comprehensive coverage while focusing resources on the most significant business risks.
Successful IT audit implementation requires careful balance between thorough examination and practical resource constraints. Organizations achieve best results by adopting risk-based approaches that prioritize high-impact areas while maintaining adequate coverage of regulatory requirements. Regular execution of this process helps businesses adapt to evolving threats while demonstrating commitment to stakeholders and regulators.
The evolving technology landscape continues to create new audit challenges and opportunities. Organizations that proactively adapt their audit processes to address emerging risks and leverage advanced capabilities will maintain stronger security postures and more effective compliance programs than those relying solely on traditional approaches.