If you’re trying to figure out the difference between vulnerability assessment vs penetration testing, you’re not alone. Most business leaders struggle with this decision, and it’s a critical one. Here’s why it matters: companies take an average of 277 days to discover and contain a data breach, and by that time, the damage averages $4.45 million, according to IBM’s 2024 Cost of a Data Breach Report. The choice between vulnerability assessment vs penetration testing—or knowing when you need both—could determine whether your organization avoids becoming part of this expensive statistic.
Think of the vulnerability assessment vs penetration testing question this way: one finds the problems, the other proves whether those problems can actually hurt your business. Both play essential roles in your IT audit services strategy, helping you meet compliance requirements, answer tough questions from your board, and actually protect the customer data and business systems you’re responsible for. This guide breaks down what each security test does, when you need them, and how to make smart investment decisions that protect your organization without wasting budget on the wrong approach.
What Is a Vulnerability Assessment?
Think of a vulnerability assessment as a comprehensive health check for your technology systems. Just like a doctor runs standard tests to identify potential health issues, a vulnerability assessment scans your networks, applications, and systems to find security weaknesses before hackers can exploit them. These assessments use specialized software tools to examine thousands of potential security gaps across your entire IT environment.
Here’s what happens during a vulnerability assessment. Security teams use automated scanning tools to check every system, application, and network device in your organization. These tools compare your systems against databases of known security flaws, things like outdated software, weak passwords, misconfigured settings, or missing security patches. The scan generates a report that lists every vulnerability found, ranks them by severity, and recommends fixes.
The real value comes from the prioritization. Not all vulnerabilities pose the same risk to your business. A security flaw in your customer payment system demands immediate attention, while a minor issue in an internal testing environment can wait. Vulnerability assessments help your security team focus limited time and budget on fixing the problems that actually threaten your operations.
Most organizations run vulnerability assessments monthly or quarterly. Companies handling sensitive data, like healthcare providers with patient records or retailers processing credit cards, often scan continuously. This regular scanning catches new vulnerabilities as they emerge, which happens constantly as hackers discover new attack methods and software vendors release patches.
The reports your team receives include clear summaries designed for executives and board members. You’ll see charts showing how many critical, high, medium, and low-risk vulnerabilities exist, which systems are most vulnerable, and trending data showing whether your security posture is improving or declining over time. These reports provide the evidence auditors and regulators need to verify you’re managing cybersecurity risk appropriately.
What Is Penetration Testing?
Penetration testing takes security validation to the next level. While vulnerability assessments identify potential problems, penetration testing proves whether those problems actually put your business at risk. Think of it as hiring professional “ethical hackers” to break into your systems the same way criminals would, except these experts work for you and report back on exactly how they got in.
Here’s the difference that matters to business leaders. A vulnerability scan might flag fifty potential security issues. But which ones actually allow someone to steal customer data, access financial systems, or shut down operations? Penetration testing answers that question by attempting to exploit the vulnerabilities to see what damage could occur.
Professional penetration testers spend weeks studying your systems, looking for creative ways to bypass security controls. They don’t just run automated tools, they think like criminals, chaining together multiple small weaknesses to achieve major breaches. For example, they might use a low-risk vulnerability in one system to gain a foothold, then leverage that access to move through your network until they reach your most valuable assets.
The testing comes in different forms depending on your needs. “Black box” testing gives testers no inside information, simulating an external hacker attack. “White box” testing provides full system documentation, allowing comprehensive security analysis. “Gray box” testing falls somewhere in between, replicating scenarios where attackers have gained limited insider knowledge.
Many regulations specifically require penetration testing. If your organization processes credit cards, PCI-DSS mandates annual penetration tests. Healthcare organizations handling patient data need regular testing under HIPAA. Companies pursuing SOC 2 certification, increasingly required by enterprise customers, must demonstrate annual penetration testing as proof their security controls actually work.
The reports you receive tell a story about what could happen in a real attack. Rather than just listing technical vulnerabilities, penetration test reports explain the business impact: “An attacker could access customer payment data,” or “Someone could gain administrator access to financial systems.” This context helps executives and boards understand the real-world consequences and make informed decisions about security investments.
Key Differences That Matter for Your Business
Let’s be clear about what separates these two approaches, because the distinction affects both your budget and your security strategy. Vulnerability assessments cast a wide net, quickly identifying potential problems across your entire IT environment. Penetration testing goes deep, proving whether specific systems can withstand actual attack attempts.
Here’s a practical analogy. Vulnerability assessments are like having a home inspector walk through your house, pointing out that your windows don’t lock properly, your doors have weak hinges, and your alarm system is outdated. Valuable information, but you don’t know if someone could actually break in. Penetration testing is like asking a professional locksmith to actually try breaking into your home using any method they can think of. When they succeed and show you exactly how they did it, you know precisely what needs fixing.
The timeline and cost differences are significant. Vulnerability assessments typically take a few days and cost $2,000 to $8,000 for small-to-medium sized businesses. Many organizations purchase annual subscriptions for continuous monitoring. Penetration testing requires several weeks and typically costs $15,000 to $50,000 or more, depending on how many systems you’re testing and how complex your environment is.
Both approaches serve different compliance needs. Vulnerability assessments provide the ongoing monitoring evidence that regulators want to see, proof you’re paying attention to security throughout the year. Penetration testing provides the point-in-time validation that auditors require, proof your security controls actually prevent breaches rather than just existing on paper.
Quick Comparison
| What You’re Comparing | Vulnerability Assessment | Penetration Testing |
| What It Does | Finds potential security weaknesses | Proves weaknesses can be exploited |
| How It Works | Automated scans with expert review | Skilled hackers manually test your defenses |
| Coverage | Everything in your IT environment | Focused on your most critical systems |
| How Often | Monthly or quarterly | Once or twice per year |
| Time Required | 1-5 days | 2-4 weeks |
| Investment | $2,000-$8,000 | $15,000-$50,000+ |
| Business Disruption | Minimal | Moderate (needs planning) |
| What You Get | List of vulnerabilities ranked by severity | Story of how hackers could breach your systems |
| Compliance Value | Ongoing monitoring proof | Control effectiveness proof |
When Your Organization Needs Vulnerability Assessments
Vulnerability assessments make sense in several specific situations. If you’re establishing a security program from scratch, start here. You need to understand your current security posture before making improvement plans. The assessment reveals the full scope of your security challenges and helps you build a realistic remediation roadmap and budget.
Schedule vulnerability assessments 2-3 months before any major audit or compliance certification. Discovering critical security gaps during the audit creates problems, auditors question why you didn’t catch these issues earlier, and you face potential failed controls or delayed certifications. Finding and fixing issues beforehand demonstrates proactive security management and saves embarrassing conversations with auditors and board members.
Organizations with limited security budgets should prioritize vulnerability assessments first. You get comprehensive visibility into security weaknesses across your entire environment without the significant investment required for penetration testing. Small security teams can monitor much larger IT environments through automated scanning than they could through manual testing.
Run vulnerability assessments after any major technology changes. Just deployed a new application? Migrated systems to the cloud? Restructured your network? These transitions often introduce security misconfigurations, default passwords that weren’t changed, overly permissive access controls, or exposed management interfaces. Catching these issues before systems go into production prevents vulnerabilities from reaching your live environment where hackers could exploit them.
Regular vulnerability scanning also satisfies the “continuous monitoring” requirements embedded in most compliance frameworks. ISO 27001, NIST Cybersecurity Framework, and industry regulations expect ongoing security vigilance, not just annual check-ups. Quarterly or monthly vulnerability assessments provide auditable proof that you maintain awareness of your security posture throughout the year.
When Your Organization Needs Penetration Testing
Some situations demand penetration testing, not just vulnerability assessments. Compliance requirements are the most straightforward driver. If you process credit card payments, PCI-DSS requires annual penetration testing, no exceptions. Healthcare organizations handling protected patient information need periodic penetration testing under HIPAA. Companies pursuing SOC 2 certification face annual penetration testing requirements from auditors examining security controls.
Your most critical business systems deserve penetration testing regardless of compliance mandates. Customer-facing applications that store personal information, financial systems that process transactions, or infrastructure supporting essential operations need validation that security controls actually prevent unauthorized access. High-value targets attract sophisticated attackers who use creative techniques that vulnerability scans can’t simulate.
Before launching major technology initiatives, conduct penetration testing. About to release a new customer portal? Completing a digital transformation project? Deploying a major system upgrade? Individual security vulnerabilities that seem low-risk in isolation can combine into critical attack paths when systems interact. Penetration testers discover these complex scenarios by attempting realistic attacks rather than evaluating vulnerabilities one at a time. Finding issues before launch costs far less than discovering them after customers are using the system.
After any security incident or data breach, penetration testing validates your remediation efforts. Incident response teams fix the specific vulnerability hackers exploited, but similar weaknesses often lurk elsewhere in your environment. Penetration testing provides assurance to executives, board members, customers, and regulators that your security posture genuinely improved rather than just patching the single hole that caused the last problem.
Organizations with mature security programs use annual penetration testing as independent verification that security investments deliver real protection. Boards of directors increasingly ask tough questions about cybersecurity: “How do we know our security controls actually work?” Penetration testing provides credible answers by demonstrating that your defenses withstand actual attack attempts.
Why Smart Organizations Use Both Approaches
The most effective security programs don’t choose between vulnerability assessments and penetration testing, they use both strategically. Think of vulnerability assessments as your routine monitoring system, continuously checking for problems. Penetration testing serves as your periodic deep-dive validation, proving your defenses work against real-world attacks.
Here’s the strategic approach that works. Start with vulnerability assessments to find and fix obvious security gaps. There’s no point paying penetration testers to exploit vulnerabilities that scanning already identified. Once your vulnerability management process matures and critical findings receive timely fixes, add penetration testing to validate that your remediation efforts actually closed attack pathways.
Most organizations run vulnerability assessments quarterly or monthly for general infrastructure, with annual penetration testing focused on critical systems. This cadence balances cost-effectiveness with comprehensive risk management. You maintain continuous visibility into emerging threats while periodically validating that security controls prevent actual compromise.
The combination directly supports your IT audit and compliance programs. Vulnerability assessments prove security control design, you have processes to identify weaknesses. Penetration testing proves security control effectiveness—those processes actually prevent breaches. Auditors examining your control environment need both types of evidence to sign off on your security posture.
The two testing methods also create valuable feedback loops. Vulnerability assessment findings help penetration testers focus on the most promising attack vectors. Penetration testing results reveal gaps in vulnerability management, when testers exploit vulnerabilities that scanning missed, your team improves coverage. When vulnerability assessments identify critical issues that penetration testers confirm can’t be exploited due to compensating controls, you gain confidence in your defense strategy.
From a business perspective, the integrated approach reduces overall risk while providing measurable return on investment. You identify vulnerabilities before hackers exploit them, validate that security spending actually prevents breaches, and maintain the documented evidence that boards, auditors, and regulators demand. Organizations that suffer breaches despite security investments face uncomfortable questions. Combined testing programs provide evidence that controls receive systematic validation.
How IT Audit Services Strengthen Your Security Testing Program
Professional IT audit services help business leaders navigate these security testing decisions strategically. Many organizations struggle to determine optimal testing frequency, define appropriate scope, or allocate budgets between vulnerability assessments and penetration testing. External IT auditors provide independent perspective on whether your current testing approach adequately addresses your risk profile compared to industry standards.
Independent auditors validate that your security testing program meets professional standards. Organizations conducting only internal testing sometimes develop blind spots or unconscious biases that prevent objective security evaluation. External auditors verify that testing scope covers all critical systems, methodologies align with industry frameworks, and findings receive appropriate attention and remediation. This independent validation strengthens stakeholder confidence that your security testing provides genuine risk visibility.
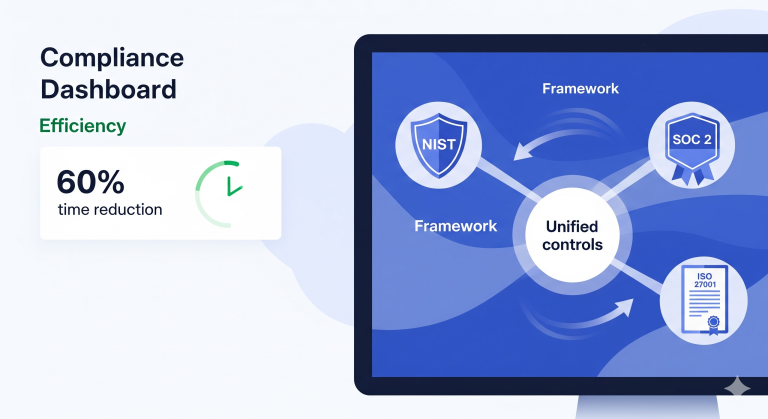
IT audit professionals also map security testing requirements across multiple compliance frameworks, eliminating wasteful redundancy. Organizations subject to SOC 2, ISO 27001, PCI-DSS, and HIPAA often conduct separate testing for each framework, spending unnecessarily on overlapping requirements. Auditors design integrated programs where single assessments satisfy multiple compliance obligations, maximizing budget efficiency while maintaining thorough security validation.
Auditors ensure your security testing documentation meets the evidence standards that external auditors and regulators require. Proper documentation includes clear scope definitions, methodology descriptions, findings classifications, and remediation tracking. Incomplete documentation can result in qualified audit opinions or failed certifications even when technical testing is sound. IT audit services keep your program audit-ready.
Perhaps most valuable for executives, IT audit services translate security testing results into business context. Technical vulnerability reports and penetration test findings get converted into board-level summaries that explain business impact, quantify risk exposure, and recommend prioritized actions. This translation helps executive teams make informed decisions about security investments and risk acceptance.
Common Questions Business Leaders Ask
Should we do penetration testing or vulnerability assessments first?
Start with vulnerability assessments unless compliance requirements force immediate penetration testing. Vulnerability assessments identify the obvious security gaps across your entire environment quickly and cost-effectively. Fix those issues first, then bring in penetration testers to validate that your remediation efforts actually closed attack pathways. Paying penetration testers to exploit vulnerabilities that scanning already found wastes budget. The exception: if PCI-DSS, HIPAA, or SOC 2 compliance deadlines are approaching, schedule penetration testing immediately to meet regulatory timelines.
How often do we really need to do this testing?
For vulnerability assessments, quarterly scanning works for most organizations, with monthly scans for companies handling sensitive data like healthcare records or payment information. Critical infrastructure should implement continuous scanning. For penetration testing, annual testing satisfies most compliance requirements and provides adequate validation for mature security programs. Add penetration testing after major system changes, following security incidents, or before launching significant new applications.
Can we skip penetration testing if our vulnerability assessments look good?
Unfortunately, no. Vulnerability assessments and penetration testing serve different purposes. Even organizations with excellent vulnerability management programs need penetration testing because assessments can’t predict how multiple vulnerabilities combine into critical attack chains. More importantly, most compliance frameworks including PCI-DSS, SOC 2, and HIPAA explicitly require penetration testing. Auditors need proof that security controls prevent actual exploitation, which only penetration testing provides.
What should we expect in the final reports?
Vulnerability assessment reports include lists of security weaknesses organized by severity, showing which systems are affected and providing fix recommendations. Executive summaries include charts and trends showing whether security posture is improving. Penetration test reports tell the story of how testers compromised systems, including proof like screenshots, descriptions of what data they accessed, and analysis of business impact. Both report types should include executive summaries written for non-technical audiences and detailed technical sections for your security team.
How do we prepare the organization for penetration testing?
Start by getting explicit authorization from executive leadership and legal counsel—penetration testing involves authorized hacking attempts that could disrupt operations. Define clear boundaries about which systems testers can target and which are off-limits. Coordinate with IT operations to schedule testing during low-impact periods. Brief your security team so they can distinguish testing activity from real attacks. Most importantly, prepare executives for findings—penetration tests typically discover exploitable vulnerabilities, and leadership needs realistic expectations about results.
Making the Right Security Testing Investment
Understanding the difference between vulnerability assessments and penetration testing helps you make smart decisions about protecting your organization. Vulnerability assessments provide the ongoing monitoring that keeps you aware of emerging security problems across your entire IT environment. Penetration testing validates that your security investments actually prevent breaches rather than just creating paperwork.
Most organizations benefit from using both approaches strategically. Regular vulnerability assessments catch security issues early, while periodic penetration testing proves your defenses work against real-world attacks. This combination satisfies compliance requirements, provides evidence for audit programs, and gives executives and boards confidence that security spending delivers measurable protection.
The integration of both testing methods within your broader IT audit program ensures security testing aligns with business objectives, meets regulatory requirements, and provides the documented evidence that stakeholders demand. Professional IT audit services help you develop the right testing strategy for your organization’s specific risk profile, compliance obligations, and budget constraints.